Product Demos
ThreatLocker Platform
Overview followed by a deep dive into ThreatLocker's Elevation Control: A unified approach against exploitation of Zero Day vulnerabilities
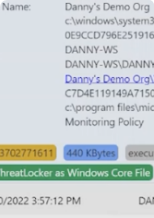
Application Allowance
Using ThreatLocker to control application execution
Elevation Control
Managing user permissions per application with Elevation Control
Network Access Control
An endpoint NAC solution to control access at the local level
5 Minute Highlights Tour
A quick overview of ThreatLocker's full capabilities
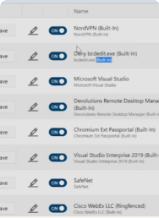
Ringfencing
Limiting application interactions with Ringfencing
Storage Control
Granular control over who and what can access your important shares
Additional Resources

 Play Now
Play Now